DDoS Technology Hardening
Our DDoS Hardening service strengthens your technology infrastructure to maximize protection against the most sophisticated DDoS attacks. Our experts analyze your current setup and provide detailed recommendations for network architecture improvements, DDoS appliance configuration optimization, and DDoS vendor selection.
Network architecture
We begin by auditing your current DDoS network architecture infrastructure. Our experts identify weaknesses and provide recommendations for improving the underlying architecture to maximize DDoS protection. This step is taken regardless of any specific vendor and is intended to ensure that your protection foundation includes the right components at the right locations.

We begin by defining the optimal protection architecture and examining all locations – web/infrastructure, on-premises, and ISPs. This foundation step takes place regardless of the specific vendor solutions.
Technology Hardening
Strengthen your infrastructure against DDoS attacks.
Error: Contact form not found.
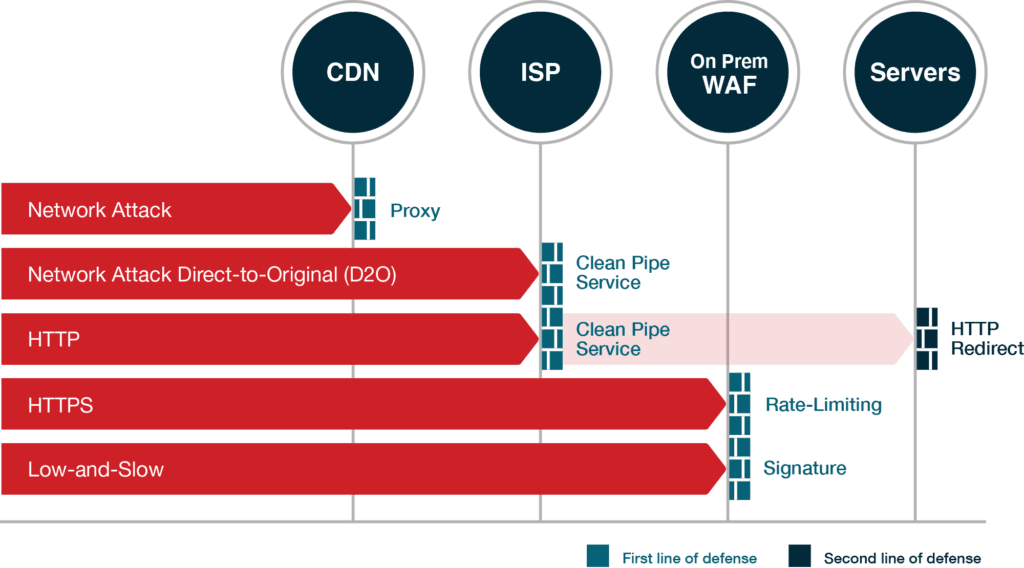
Next, we conduct an analysis of attack vectors. We analyze all potential DDoS attacks and determine how each type will be handled by the protection components in your recommended architecture.
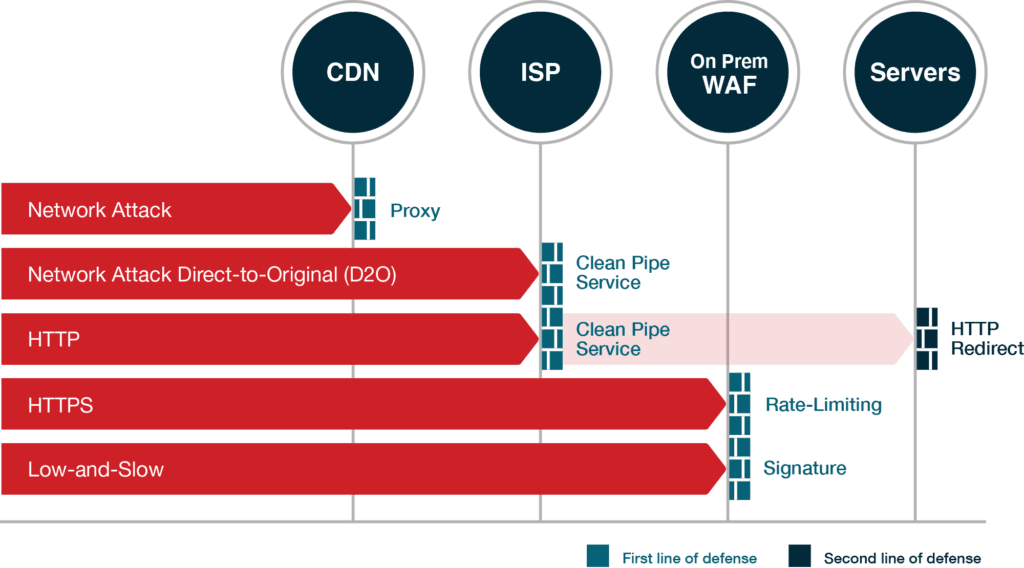
The attack vector analysis outlines the potential DDoS attacks on your systems and describes how each attack type will be handled by the different components in your protection architecture. The diagram is for demonstration purposes and is a simplified version of actual analysis.
Configuration optimization
Installed DDoS protection gear is often underutilized. Our team dives into the setup of your protection solution(s) and provides detailed instructions on improvements to their configuration.
For example, we ensure that rate limit thresholds are well-calibrated, that you have chosen the most appropriate web challenge, that you fully utilize bot protection, geo-protection, etc.
Vendor selection
As a vendor-agnostic consulting company, we are deeply knowledgeable about the capabilities of all DDoS vendors and can help select the DDoS protection solution that best meets your needs, thereby saving your team many man-hours.
Vendor selection is an optional service, which may be purchased separately from the core Hardening service. Our DDoS experts guide you through a meticulous and methodical vendor evaluation, using an RFP template that includes over 80 selection criteria, with the ability to adjust the weight for each requirement and assign scores to vendors. In addition, we provide a recommendations document presenting several DDoS vendor options that are most suitable for your requirements, with an analysis of the pros and cons of each in relation to your architecture and needs.
DDoS Hardening Solution Brief
Case study: Hardening the technology of a large bank against DDoS