AWS DDoS Testing
Validate your system’s DDoS protection on AWS

DDoS Testing Tailored
to Your AWS Deployment
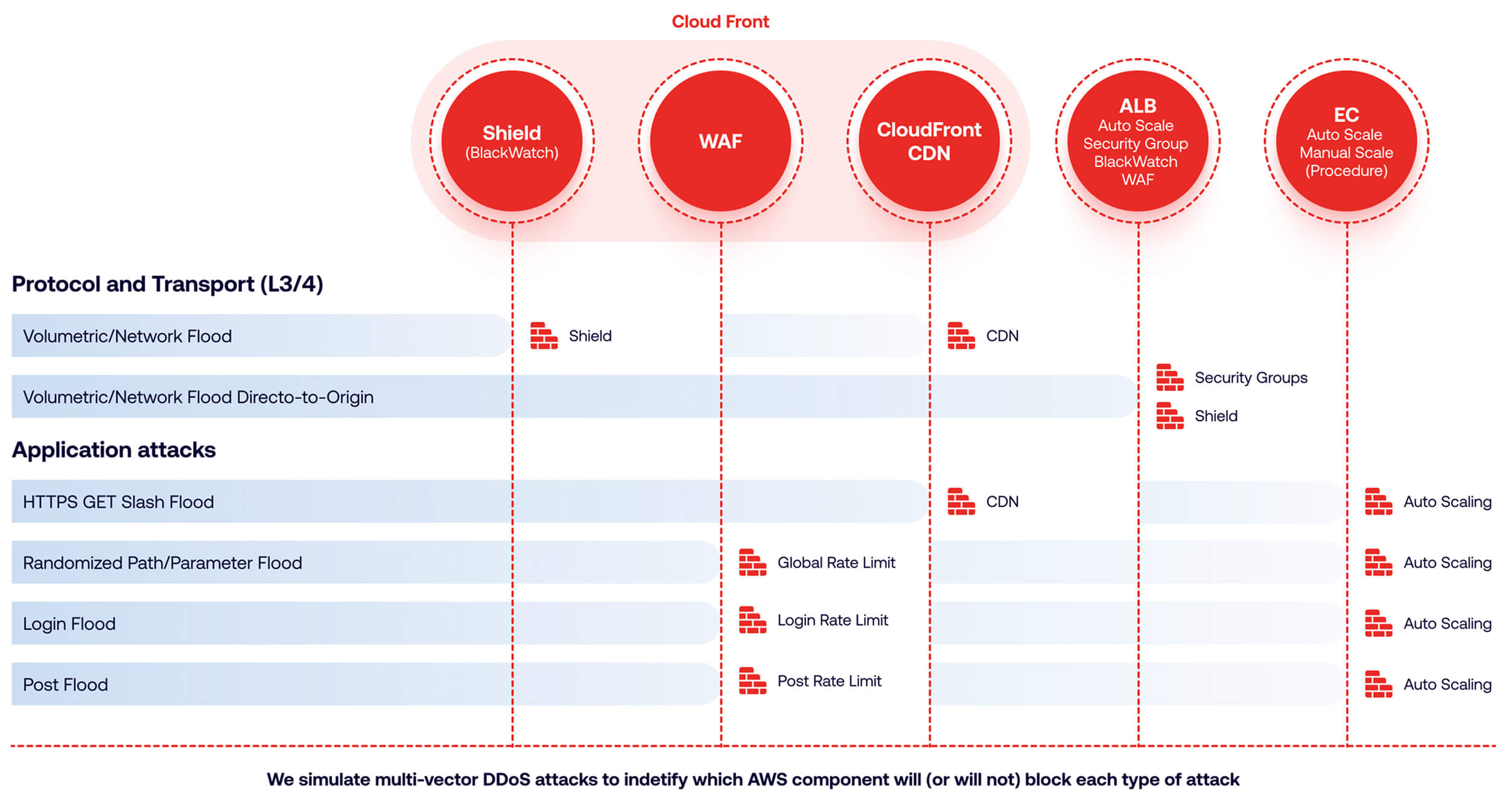
Verify your DDoS protection with attack simulations that challenge your specific deployment architecture. If your deployment includes CloudFront with ALB and EC2 behind it, for example, then we’ll run an attack simulation quite different from the one we’d plan if you had an API Gateway and AWS Lambdas.
Actionable
Remediation Guidance
Following a DDoS simulation, you’ll receive:
- A detailed report identifying all security flaws, prioritized by severity. (See a sample test report)
- Remediation recommendations – from optimal configuration of AWS WAF options to the addition of specific security components.
- An optional re-testing session to validate the fixes you implemented.

Get Results with
Near-Zero Efforts
Our fully managed DDoS testing service saves you time and resources:
- End-to-end test planning, execution and analysis by highly experienced DDoS experts.
- A total of five hours of your time: One hour for pre-test interview, three hours for test session, one hour for reporting the results and our recommendations.

FAQ
DDoS 360 is a fully managed, expert-led DDoS resilience program built for high-risk organizations that must prove operational readiness and maintain continuous availability. Instead of one-off tests, it operates as a continuous improvement cycle consisting of Testing, Hardening, Retesting, and Training, plus dedicated Incident Response support. This process continuously validates your defenses against real-world scenarios while placing minimal operational burden on your internal teams.
Simply having tools is rarely enough; in fact, 75% of companies fail to mitigate severe DDoS attacks. This high failure rate is primarily driven by overconfidence, untested defense mechanisms, underutilized protection technologies, and a lack of team training on how to identify and mitigate attacks. Continuous testing ensures your expensive anti-DDoS tools are correctly configured to handle evolving threats.
Our simulations are incredibly realistic, executed safely using a proprietary distributed botnet platform spanning over 30 countries. We can simulate massive real-world conditions, including attack volumes up to 300 Gbps, up to 5 Million Packets Per Second (PPS), and up to 500,000 HTTP Requests Per Second (RPS) using a fleet of up to 1,000 attacking botnets and over 100 distinct attack vectors.
We utilize three primary testing methodologies depending on your goals:
- Blackbox: Simulates an external attacker with no prior system knowledge, which is ideal for real-world simulation, external pen-testing, and regulatory audits.
- Whitebox: Grants us full visibility into your architecture for a deep-dive analysis, best suited for secure SDLC and architectural hardening.
- Graybox: Utilizes partial system knowledge, offering the best of both worlds for insider threat simulation and hybrid environments.
The DDoS Resiliency Score (DRS) is a core metric included in our expert reporting. It measures your current protection level against your desired industry benchmark and your competition. Over successive testing and hardening cycles, you will see your DRS improve as security flaws are closed.
A DDoS attack scenario is a distinct simulation configuration that combines a specific attack vector with defined targets. For example, pairing an HTTP GET Flood (the vector) against a specific application URL (the target) equals one scenario. Depending on your tier, we safely run between 6 and 12 distinct attack scenarios per testing session to stress-test different parts of your infrastructure.
