DDoS Ransom Attack on a Latin American Bank
Background
A Latin American conglomerate, which includes a bank and several financial companies, received an extortionary email threatening to carry out a DDoS attack. The hacker group demanded Bitcoin payment and warned they would attack in one week if money was not received.
Nevertheless, the first DDoS attack started the same day that the threatening email arrived. Afterwards, the company engaged Red Button’s Incident Response team to prepare for and mitigate further attacks.
Attack Timeline
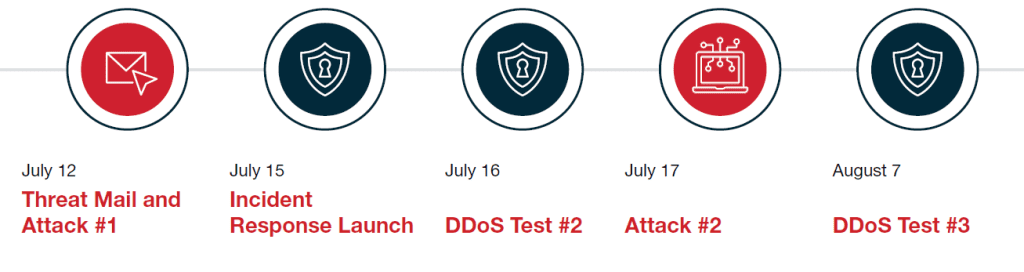
Threat mail and attack #1
The first DDoS attack was 60 Gbps, launched the same day the extortion message was received, using a UDP reflection attack vector. The company’s internal security and IT teams activated mitigation measures, which involved diverting traffic to the DDoS Mitigation provider Imperva Incapsula. A few network segments that were initially unprotected were the source of a 15-minute disruption of service due to pipe saturation. However, once the traffic was diverted, all services returned to their normal state.
Incident response and DDoS test #1
Following the first attack, the company engaged Red Button’s Incident Response team. Our personnel met with all the company’s relevant in-house teams to review their DDoS protection architecture. Several hours later, we ran a controlled DDoS network attack simulation to detect and fix vulnerabilities. The simulation uncovered multiple problems with infrastructure protection and the routing of traffic to Imperva Incapsula. The IT team was then tasked with fixing the identified issues.
Test #2
The next day, our team repeated the simulation and ran another controlled network DDoS attack. The routing problems were all fixed and the simulated attack was stopped successfully.
DDoS attack #2
The attackers launched a second attack. While the company’s team and its protection measures were fully prepared for a larger, more extensive assault, the second incident was almost identical to the first – a 60Gbps volumetric attack lasting 24 hours. Thanks to the testing and fixes implemented earlier, as well as the collaboration between the company’s IT team and our Incident Response experts, the attack was fully mitigated, with zero service disruptions.
Test #3
After the deadline set by the hackers had passed and no additional attacks were identified, our team ran another simulation. This was intended to test the mitigation of application-level DDoS attacks. Our team identified configuration gaps in the Imperva web protection system and helped the company’s IT team to close them.
Conclusion and Recommendations
Following the incident response and mitigation activities, our team provided the company with a detailed report containing conclusions and recommendations, including:
- Run periodic DDoS simulations (including application protections).
- Add or harden application protections.
- Add an external managed DNS service.
- Configure automatic traffic diversion to reduce the time-to-mitigation.
Read Other
Case Studies
Check out these resources for more information
about our DDoS testing solutons for your business.