| Family | Network Attacks |
| Attack Vector | ACK Flood |
| Variants | – |
| DRS ID | 14008 |
| Supports spoofing | Yes |
| Capture file example |
| Tools | Hping |
Description
TCP ACK flood, or ‘ACK Flood’ for short, is a network DDoS attack comprising TCP ACK packets. The packets will not contain a payload but may have the PSH flag enabled.
In the normal TCP, the ACK packets indicate to the other party that the data have been received successfully. ACK packets are very common and can constitute 50% of the entire TCP packets.
The attack will typically affect stateful devices that must process each packet and that can be overwhelmed.
ACK flood is tricky to mitigate for several reasons. It can be spoofed; the attacker can easily generate a high rate of attacking traffic, and it is very difficult to distinguish between a Legitimate ACK and an attacking ACK, as they look the same.
Impact
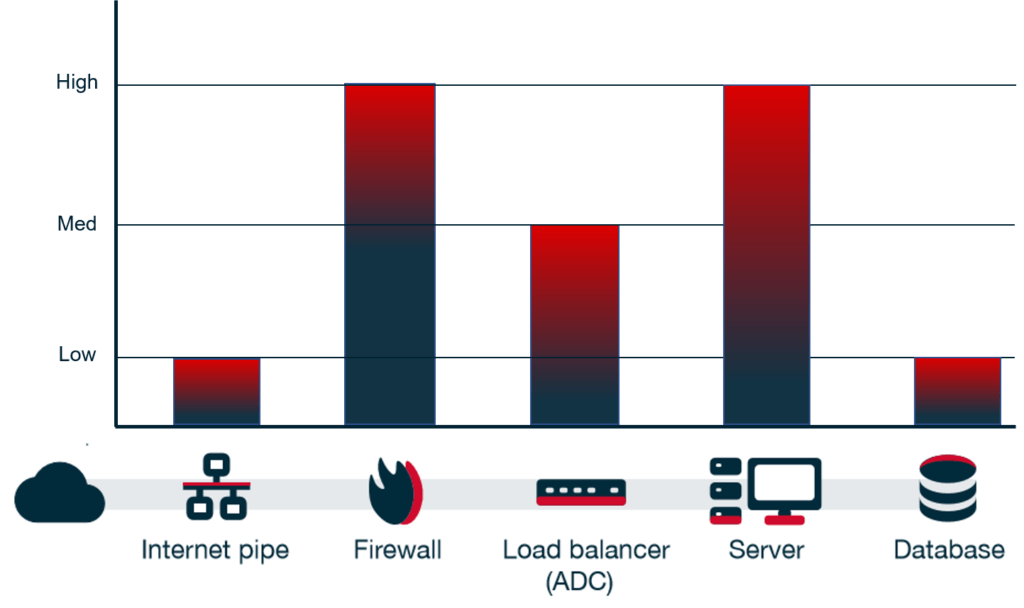
ACK flood will typically affect stateful devices, such as a firewall and web servers that must invest resources into processing the ACK packet. Because these packets are not linked to any session on the server’s connection list, the server spends more resources on processing these requests. The result is a server that is unavailable to process legitimate requests due to exhausted resources while the attack is ongoing.
Mitigation
| Technology | Description |
| Challenges | |
| Proxy | ✔ |
| State/Anomaly protection | ✔ |
| Caching | |
| Rate limit | |
| Signatures | |
| Behavioral |
A strong proxy-based technology (for example, CDNs) that protects the targeted server will prevent the attack from reaching the targeted servers because the ACK packets are not part of a legitimate connection and therefore will not pass the proxy (so long as the proxy mitigation is strong enough to handle the attack rate).
In a similar manner, State/Anomaly protection can also mitigate the attack, as the ACK packets are anomalous. (They do not belong to a valid session.) This applies so long as they have the capacity to handle the attack rate.